VLAN (virtual local area network) is essentially a network within a network. It is a network topology in which a collection of connected devices are logically grouped into distinct broadcast domains, even if they are not located in the same physical location. It is used as an effective way to segment networks for security or efficiency purposes.
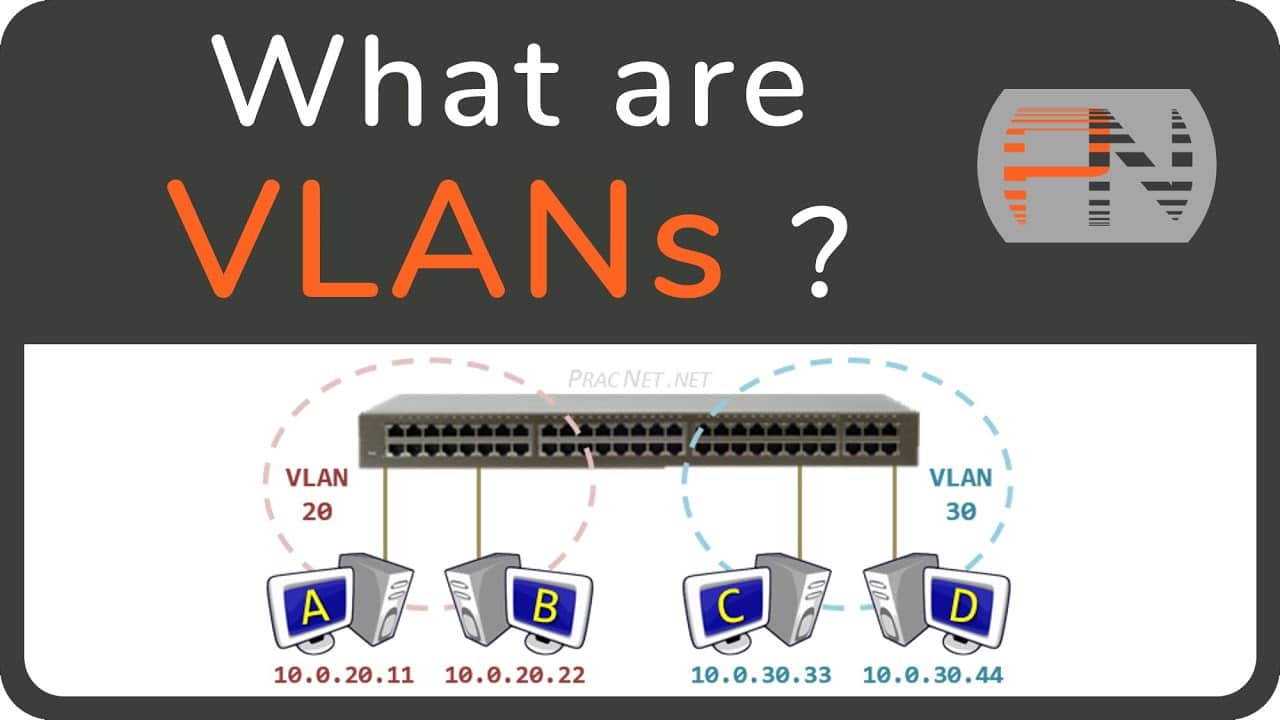
Every device in a VLAN will belong to a given broadcast domain. This broadcast domain is determined by the device’s type and is independent of the actual physical location within the network. This means that devices connected to the same switch can belong to different VLANs.
VLANs can speed up network traffic, since each VLAN is only allowed to send and receive broadcast messages within its own broadcast domain. This is because by default, devices in different VLANs cannot communicate with each other since they are unaware of each other’s existence. To share information across VLANs, an inter-VLAN routing protocol will need to be used.
VLANs are commonly used in corporate environments as a means of optimizing network usage and security. For instance, a VLAN can be used to keep confidential data separate from more public information. VLANs are also used in public places such as hotels or universities to segment users into different broadcast domains. Here, a VLAN can be used to manage user bandwidth allotments or grant different user access to different services or websites.
VLANs are beneficial in terms of security, scalability, and flexibility. By creating virtual boundaries within a physical network, VLANs allow more precise control over broadcast traffic and the separation of critical data from less sensitive information. Additionally, VLANs allow for efficient network management, as they can be rapidly scaled to accommodate a larger number of endpoints as the network grows.
Overall, VLANs are an important network topology and are useful for organizations looking to optimize their networks for speed, efficiency, and security. They provide a range of benefits, including improved scalability, more efficient resource management, and enhanced security.